Article summary
VPNs are great for protecting your security when you’re on a network that you can’t trust completely, such as coffee shop or conference WiFi. However they don’t represent a complete solution by themselves. On macOS, Little Snitch can help you fill the gaps.
What’s the Problem?
Using a VPN will secure your network traffic while you are using it. But that still leaves two critical times:
- The span between the time you join the network and the time you activate the VPN
- Any time the VPN disconnects for some reason
In either case, the VPN isn’t active, so it isn’t protecting your network communication. These cases may seem small, but ask yourself: Could any of your applications reach out via the network before you
activate the VPN? If your VPN disconnects for some reason, will you notice?
It would be ideal if you had a way to mark a network as untrusted and not allow any network connections until you establish a VPN connection.
Enter Little Snitch
Little Snitch is basically a firewall that allows you to control which of your programs can make outgoing network connections, and which servers they are allowed to communicate with. The first time an application makes a network request, Little Snitch prompts you for approval.
It’s also really handy for testing offline behavior while developing mobile applications.
Two relevant features that Little Snitch provides are Profiles and Automatic Profile Switching. Profiles are collections of rules regulating which applications are allowed to connect to which servers, and Automatic Profile Switching allows for selecting the currently active profile based on, e.g., the current WiFi network. With these features, we can configure Little Snitch to automatically block any traffic while the VPN isn’t connected.
Configuring Little Snitch
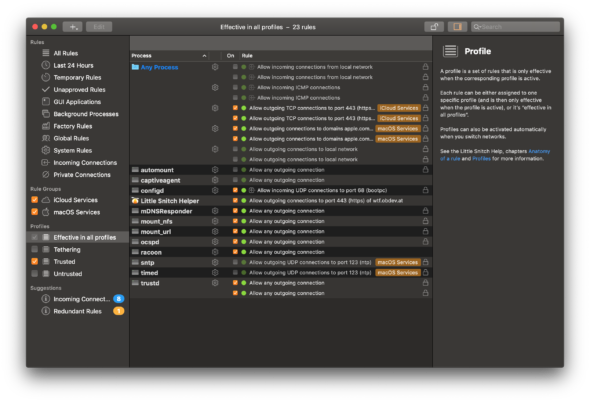
The first step is to make sure that, in the Little Snitch rule editor, only the default and system rules are present under “Effective in all profiles.” If you’ve already been using Little Snitch and have your own rules defined here, you should create a new profile and move those rules into it.
There are a couple of custom rules that should also be defined under “Effective in all profiles”:
- Allow all connections for
/usr/libexec/racoon - Allow all connections for
/usr/libexec/captiveagent
Racoon is the daemon that establishes and manages an IPSEC VPN. If you’re using a different kind of VPN, such as OpenVPN, you’ll need to add rules to allow your specific software.
Captive Agent is a feature built into macOS that will automatically attempt to detect and show a window for networks that have “captive portals,” which are common at hotels, restaurants, and other public places.
Once you’re done, your “Effective in all profiles” rules should look pretty close to this:
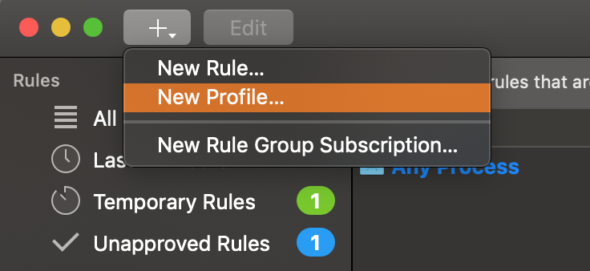
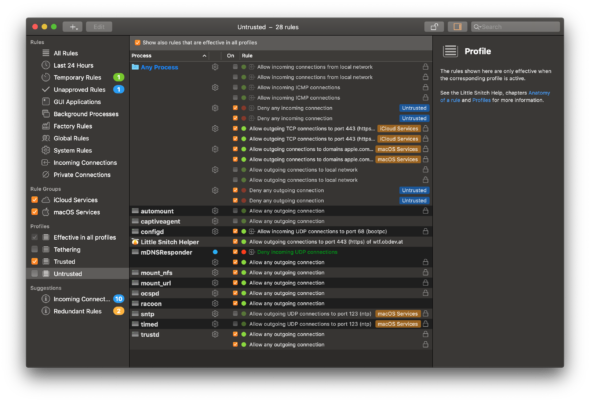
The Untrusted Profile
Now we’ll set up a profile that we can activate when we connect to networks we don’t trust. Its purpose will be to deny access to basically everything. I’ve created four rules that deny both incoming
and outgoing connections to any system process or user process, but you could also just rely on Little Snitch to prompt you for permission (so that you can hit the Deny button).
The Trusted Profile
Similarly, you’ll want a trusted profile to use when you’re on networks that you do trust. Presumably, this includes your VPN. If you already had custom rules that were present in your “Effective in all profiles” section, this is where you should move them.
How you define this profile is totally up to you.
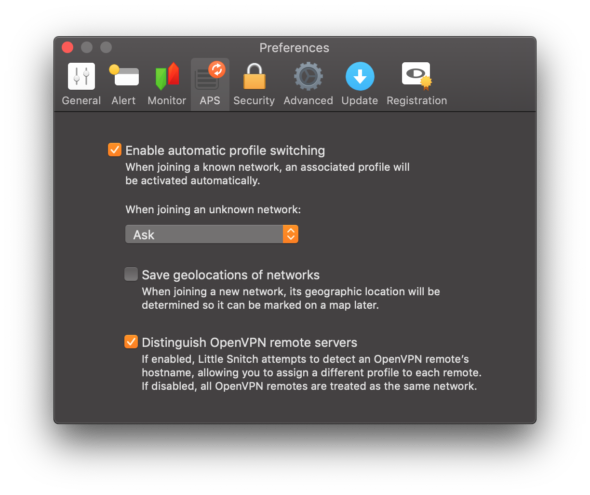
Profile Switching
Once you’ve got Little Snitch’s automatic profile switching enabled, it will prompt you to choose the appropriate profile when you join foreign networks. You should obviously choose your untrusted profile.
For both your known trusted networks and your VPN connection, you should configure the trusted profile to be selected.
Once you’ve done this, all the pieces will come together. When you are on a public network, you can select the untrusted profile, and it will block all traffic until you establish a VPN connection. After that, it will automatically switch over to your trusted profile.
Conclusion
With a bit of configuration, Little Snitch can help improve the security of your computer by making it obvious when your VPN isn’t connected. Here’s to better security.


“Racoon is the daemon that establishes and manages an IPSEC VPN. If you’re using a different kind of VPN, such as OpenVPN, you’ll need to add rules to allow your specific software.”
What would such rule be, if I were using NordVPN which uses OpenVPN?